UAE
Testvox FZCO
Fifth Floor 9WC Dubai Airport Freezone
Medical device manufacturers are facing a threat environment that has fundamentally changed. 24% of healthcare organizations were hit by medical device cyberattacks in 2026, and those attacks directly impacted patient care. That number should alarm every product team still treating cybersecurity as a final checklist item. Regulators have noticed, and the FDA has responded with guidance that makes robust security assessment a hard requirement for market entry. This guide walks you through exactly what assessors look for, what evidence you need to produce, and how to build a program that passes the first time.
| Point | Details |
|---|---|
| Regulatory requirements rising | FDA and industry demands now require robust cybersecurity evidence, not just basic safety documentation. |
| Exploitability focus | Effective risk assessments prioritize how easily vulnerabilities could be exploited, not just how likely they are. |
| Early integration matters | Integrating cybersecurity during device design leads to greater compliance and fewer product delays. |
| Maturity drives results | Companies using maturity frameworks and leadership roles outperform in audits and real-world security. |
| Evolving threat landscape | AI, IoMT, and unpatchable legacy devices require adaptive strategies and ongoing vigilance. |
The stakes here are not abstract. When a connected infusion pump gets compromised or a cardiac monitor is taken offline by ransomware, patients get hurt. Cyberattacks on medical devices are no longer rare edge cases; they are a documented, growing pattern with real clinical consequences.
“The data is clear: attacks on medical devices are rising, procurement standards are tightening, and manufacturers who treat cybersecurity as optional are being left behind by both regulators and hospital buyers.”
The numbers reinforce this urgency. 80% of medical device attacks directly impact patient care, with the primary causes being unpatched vulnerabilities and outdated operating systems. These are not sophisticated zero-day exploits. They are known, documented weaknesses that manufacturers simply failed to address.
The FDA responded by finalizing comprehensive FDA cybersecurity requirements in June 2025. This guidance requires threat modeling, assessment, and documentation for all cyber devices as part of the quality management system and premarket submission process. Compliance is no longer optional or aspirational.
The risk landscape includes several distinct threat categories:
Understanding these categories helps you scope your assessment correctly from the start. Trying to address them after design lock is where most manufacturers lose time and money. Reviewing the full landscape of compliance steps early in your product lifecycle will save you significant rework later.
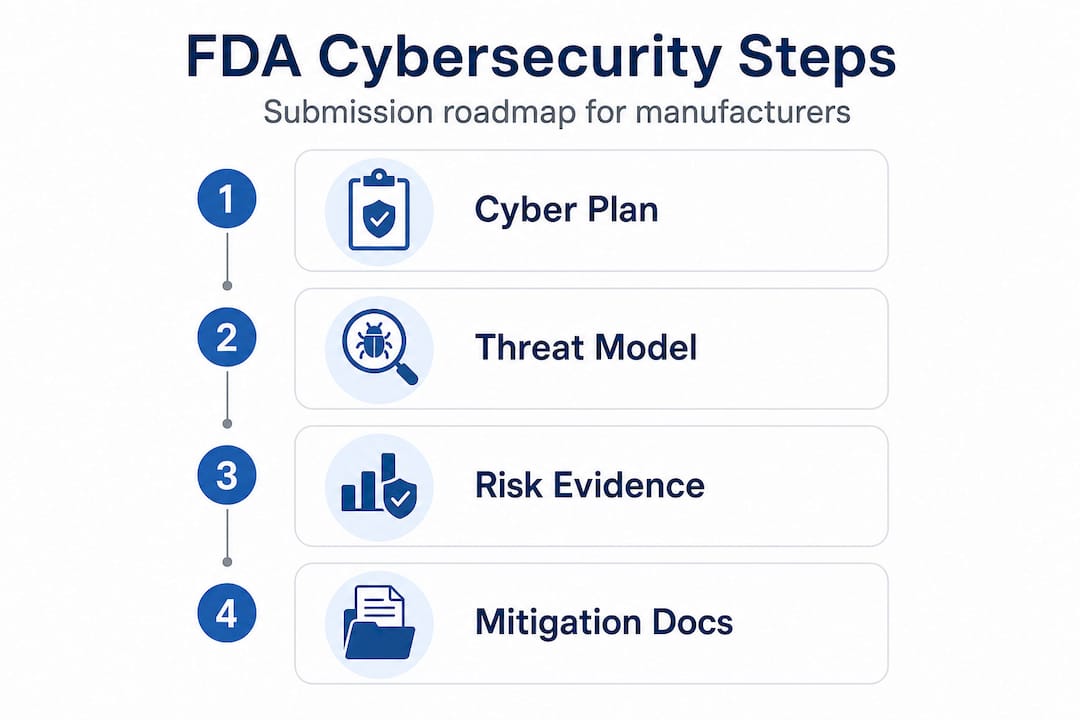
The FDA’s 2025 guidance is specific about what manufacturers must submit. Vague security statements and generic risk matrices will not satisfy reviewers. You need structured, traceable evidence that maps directly to your device’s threat landscape.
Here is a side-by-side comparison of traditional safety assessment versus modern cybersecurity assessment to clarify the shift:
| Assessment dimension | Traditional safety assessment | Modern cybersecurity assessment |
|---|---|---|
| Focus | Physical hazards and failure modes | Cyber threats, exploitability, and attack surfaces |
| Risk scoring | Severity and probability | Pre/post-mitigation exploitability scoring |
| Documentation | Design history file, risk management file | Cybersecurity management plan, SBOM, threat model |
| Testing method | Bench testing, simulation | Penetration testing, fuzzing, static/dynamic analysis |
| Ongoing obligation | Post-market surveillance | Continuous monitoring, patch management, SBOM updates |
| Regulatory standard | ISO 14971 | FDA 2025 guidance, UL 2900-2-1, NIST frameworks |
The FDA’s 2025 guidance specifies required evidence including threat modeling, a software bill of materials (SBOM), and a cybersecurity risk assessment tied directly to exploitability. Here are the core required elements for your submission:
One critical point that catches many manufacturers off guard: FDA may reject substantial equivalence if cybersecurity risks are inadequately addressed. This means a weak cybersecurity submission can block your entire 510(k) clearance, regardless of how strong your clinical or safety data is. Review our penetration testing guide for a detailed breakdown of what structured testing looks like in practice.
Understanding exploitability-based risk is worth a moment of extra attention. Traditional risk assessment asks: “How bad would it be if this failed?” Exploitability-based assessment asks: “How easy is it for an attacker to make this fail?” A vulnerability with moderate severity but trivial exploitability is actually a high-priority risk. Many teams using legacy ISO 14971 frameworks miss this distinction entirely, which is why their submissions get flagged. Our risk assessment frameworks page covers the specific methodologies that align with FDA expectations.
Pro Tip: Start building your cybersecurity documentation during the design phase, not after design freeze. Retrofitting threat models and SBOMs onto a finished design is painful, expensive, and usually obvious to experienced auditors. Documentation that grows with your design is far more credible.
Knowing what documents you need is only part of the challenge. The harder part is building the organizational processes that produce those documents reliably and keep them current. Here is a practical sequence for getting audit-ready:
The following table summarizes common device vulnerabilities and the recommended patch strategies:
| Vulnerability type | Common cause | Recommended mitigation |
|---|---|---|
| Unpatched OS components | End-of-life software, infrequent update cycles | SBOM tracking, automated patch alerts, EOL planning |
| Hardcoded credentials | Development shortcuts carried to production | Secure credential management, pre-release code review |
| Insecure communication | Unencrypted data transmission | TLS enforcement, certificate pinning |
| Weak authentication | Default or single-factor login | Multi-factor authentication, session management controls |
| Third-party library flaws | Outdated dependencies | Automated dependency scanning, SBOM-linked alerts |
| Insufficient logging | No audit trail for access or changes | Centralized logging, tamper-evident audit logs |
Pro Tip: Use threat modeling tools like Microsoft Threat Modeling Tool or IriusRisk early in your design process. Pairing these with a recognized maturity framework helps you catch architectural risks before they become expensive redesigns. Explore our penetration testing startup guide for practical guidance on scoping and executing your first formal test. Also review how to avoid compliance mistakes that commonly trip up teams during final submission reviews.
The threat landscape is not static. Three technology shifts are actively expanding the attack surface for medical devices: AI integration, cloud connectivity, and widespread remote access. Each one changes the scope of what your cybersecurity assessment needs to cover.

The MDIC 2025 Cybersecurity Benchmark confirms that AI, cloud use, and post-quantum cryptography risks are shifting security exposure toward third parties and home-use environments, complicating traditional assessment models. A device that was previously assessed as a standalone unit may now have a cloud-connected companion app, a remote monitoring portal, and an AI-driven diagnostic algorithm. Each of those components needs to be included in your threat model and tested accordingly.
Legacy devices present a separate and particularly stubborn challenge. 99% of hospitals have IoMT devices with known exploited vulnerabilities in their networks, and a staggering 60% of medical devices are end-of-life and unpatchable. That means more than half the connected devices in clinical environments cannot be fixed through traditional software updates. If your device operates in that environment, your assessment needs to account for the risks posed by neighboring devices, not just your own.
Practical mitigation tactics for these complex environments include:
For a deeper look at how to fix healthcare device gaps in complex environments, explore the specific control frameworks that apply to IoT and AI-enabled devices.
Here is what we see repeatedly when manufacturers come to us after a failed submission or a difficult audit: they treated cybersecurity as a documentation exercise rather than a security exercise. They gathered the required paperwork, checked the required boxes, and submitted. Then they were surprised when reviewers pushed back.
The core problem is that most teams still think about cybersecurity assessment the way they think about a traditional design review. You gather evidence, you present it, you pass. But cybersecurity reviewers are not just checking whether documents exist. They are evaluating whether your security posture is credible. A threat model that does not align with your actual architecture, or a penetration test that only covers obvious attack vectors, signals that your team does not genuinely understand the risk.
“Maturity leaders integrate security early, leverage the total product lifecycle, and assign clear ownership. That combination consistently outperforms teams that rely on late-stage documentation sprints.” — MDIC 2025 Cybersecurity Benchmark
Documentation retrofits are particularly damaging. When a team builds a device and then writes the threat model afterward, the threat model reflects what they built, not what they should have built. Auditors with experience can spot this pattern. The threat model will be suspiciously clean, the risks will all be neatly mitigated, and the testing scope will conveniently match the documented architecture. Real threat models are messier because real design processes are messy.
What actually works, based on what security risk assessment insights from high-performing organizations consistently show:
The manufacturers who consistently pass assessments on the first attempt are not the ones with the most sophisticated security programs. They are the ones who started early, assigned ownership, and built security into their process rather than onto their product.
If your team is preparing for an FDA cybersecurity submission or wants to close gaps before a formal audit, the path forward is clearer than it might seem.
Testvox provides security testing services specifically designed for medical device manufacturers navigating FDA compliance requirements. Our VAPT specialists understand the documentation standards, exploitability-based risk frameworks, and penetration testing protocols that regulators expect. We have worked with device manufacturers to produce audit-ready evidence packages, including threat models, SBOM reviews, and structured pen testing aligned with UL 2900-2-1. Our FDA-ready device security testing case study shows exactly how we helped a patient monitoring device team achieve compliance without last-minute surprises. Reach out to Testvox to build a testing program that accelerates your path to market.
Manufacturers must provide a cybersecurity management plan, threat modeling evidence, risk assessments based on exploitability, a software bill of materials (SBOM), and security testing results. FDA’s 2025 guidance requires all of these elements for cyber device premarket submissions.
Exploitability-based risk assessment prioritizes security risks based on how easily an adversary can exploit a vulnerability, not just the theoretical harm it could cause. FDA’s evidence requirements specifically call for pre/post-mitigation scoring grounded in exploitability.
Policies should be revisited at minimum annually, and immediately whenever a technology change, new platform integration, or significant new vulnerability affects your device’s risk profile.
Many devices run outdated operating systems, and 60% are end-of-life unpatchable, meaning traditional software updates cannot close known security gaps, leaving them permanently exposed to documented exploits.
Organizations using maturity frameworks and assigning clear ownership consistently deliver stronger compliance outcomes. Maturity leaders outperform peers in both audit performance and real-world security posture because they treat security as a program, not a project.
Let us know what you’re looking for, and we’ll connect you with a Testvox expert who can offer more information about our solutions and answer any questions you might have?