UAE
Testvox FZCO
Fifth Floor 9WC Dubai Airport Freezone
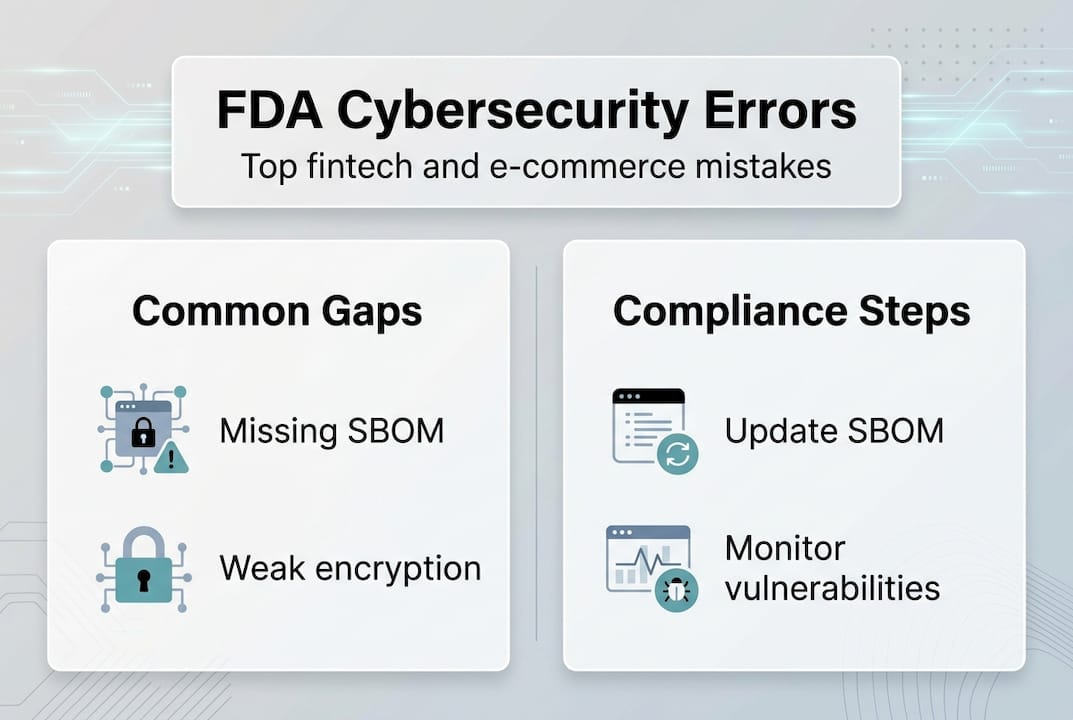
FDA cybersecurity compliance isn’t just a concern for hospital systems and medical device manufacturers. Fintech and e-commerce startups are increasingly brushing up against these rules, often without realizing it until a product launch stalls or a regulatory flag gets raised. The FDA’s expanding definition of what counts as a “cyber device” has quietly widened the net, catching founders off guard at the worst possible moments. This guide breaks down the most common FDA cybersecurity mistakes companies make, explains exactly what the regulations require, and gives you a practical roadmap to fix the gaps before they cost you time, money, or market access.
| Point | Details |
|---|---|
| FDA rules apply widely | Fintech and e-commerce apps handling medical data may be subject to FDA cybersecurity requirements. |
| Top mistakes hurt compliance | Missing SBOMs, weak documentation, and viewing compliance as a checkbox are the most common pitfalls. |
| Checklist ensures readiness | Following an actionable checklist streamlines FDA and security compliance for startups and SMEs. |
| Future-proof with best practices | Continuous monitoring, tool adoption, and process updates help maintain ongoing compliance. |
Most founders assume FDA cybersecurity is someone else’s problem. That assumption is becoming increasingly expensive. The FDA has broadened its definition of regulated “cyber devices” to include software that connects to, or interfaces with, clinical systems, health data platforms, and even certain payment or identity verification tools that touch health-related information. If your fintech or e-commerce app processes health insurance claims, integrates with wearable data, or routes any medical billing, you may already be in scope.
The regulatory pressure also isn’t static. Under Section 524B of the Food, Drug, and Cosmetic Act, companies must now provide a Software Bill of Materials (SBOM), a documented postmarket vulnerability management plan, and verified security controls. These aren’t suggestions. The FDA mandates SBOMs, vulnerability management, and security controls for any cyber device seeking market clearance. Non-compliance means your submission gets rejected or your product gets pulled.
Here’s what’s specifically new and why it matters for your team:
“Fintech and e-commerce companies that touch health-related data are no longer operating in a separate regulatory lane. FDA cybersecurity rules are a real and growing risk for any startup that underestimates scope.”
The fintech app challenges around compliance are uniquely complex because your stack typically includes multiple third-party APIs, payment processors, and data layers, each of which adds surface area for vulnerabilities and documentation gaps.
One critical data point: the FDA rejected a notable share of cyber device submissions in recent cycles specifically due to incomplete cybersecurity documentation. Getting this wrong doesn’t just delay your launch. It signals to regulators, partners, and investors that your security posture is immature.
Now that you understand the stakes, let’s get specific. These are the mistakes we see most often when working with fintech and e-commerce teams preparing for FDA review or post-market audits.
1. No SBOM, or an incomplete one. Many teams produce an SBOM only when asked, pulling it together at the last minute from memory or a single scan. This is a problem. The SBOM and vulnerability controls required under Section 524B must be accurate, version-specific, and updated with every release. Missing a single library, especially an open-source one with a known CVE (Common Vulnerability and Exposure), can be grounds for rejection.
2. No documented postmarket vulnerability management plan. You might have a smart DevSecOps setup internally, but if it isn’t written down in a format reviewers can evaluate, it doesn’t exist from a compliance standpoint. Regulators want to see a process, not just a capable team.
3. Weak security controls for data in motion and at rest. This includes inadequate TLS configurations, unencrypted database fields, or missing access control policies. These are the easiest vulnerabilities for auditors to find and the hardest to defend without prior documentation.

4. Treating compliance as a one-time checkbox. This is the most common mindset mistake. Compliance isn’t a destination. It’s an ongoing state. Teams that pass one review and then freeze their documentation quickly fall out of compliance as their software evolves.
5. Missing documentation for third-party code. Every npm package, SDK, and open-source library you use is part of your attack surface. Failing to document these is a direct violation of SBOM requirements.
Pro Tip: Run a software composition analysis (SCA) scan on your codebase right now, before your next release. Tools like OWASP Dependency-Check or Snyk will surface third-party vulnerabilities you may not know exist.
Understanding QA’s role in cybersecurity is critical here because security testing isn’t just a dev function. QA teams catch documentation gaps, misconfigured controls, and integration-level vulnerabilities that developers often miss. And the hidden costs of poor security go well beyond fines. You’re looking at delayed launches, customer churn, and loss of enterprise contracts.
“The gap between ‘we’re secure’ and ‘we can prove we’re secure’ is exactly where most FDA rejections happen.”
For lean teams wondering where to start, lightweight security testing options are available that don’t require a large internal security function to be effective.
Here’s a practical checklist mapped directly to what FDA reviewers look for. Use this to benchmark where your team stands today.
Pro Tip: Use a dependency management tool like Dependabot or Renovate to automatically flag outdated packages. This keeps your SBOM accurate without adding manual overhead to your release process.
| Category | Compliant | Non-Compliant |
|---|---|---|
| SBOM | Updated, versioned, covers all components | Missing, outdated, or partial |
| Vulnerability plan | Documented, assigned, tested | Informal or undocumented |
| Encryption | Enforced for data in motion and at rest | Partial or legacy protocols |
| Third-party code | Tracked and audited regularly | No inventory or last-minute checks |
| Penetration testing | Scheduled, logged, remediated | Ad hoc or never done |
The cybersecurity gaps that kill submissions are almost always process gaps, not technology gaps. Most teams have decent tools. Very few have the documentation to back them up. You can review how FDA-ready device security testing works in practice to understand what a full, compliant audit looks like.
The FDA’s Section 524B requirements are explicit: documentation must be defensible, traceable, and current. Make those three words your compliance mantra.
Passing today’s audit doesn’t guarantee you’ll pass next year’s. Threat landscapes change, FDA guidance updates, and your codebase grows. Here’s how to build a system that stays compliant without grinding your team to a halt.
Tools that align with FDA required controls:
| Tool category | Example tools | FDA control addressed |
|---|---|---|
| SCA (Software Composition Analysis) | Snyk, OWASP Dependency-Check, Black Duck | SBOM generation and vulnerability tracking |
| Continuous monitoring | Wazuh, Datadog Security | Postmarket threat detection |
| Penetration testing | Burp Suite, Metasploit, Cobalt Strike | Security control validation |
| SBOM management | CycloneDX, SPDX-based tools | FDA-mandated SBOM formatting |
| Secrets management | HashiCorp Vault, AWS Secrets Manager | Access control and encryption |
Beyond tools, your strategy needs to include these ongoing practices:
The security testing case studies and VAPT case studies from real product audits show one consistent pattern: teams that integrate compliance into their sprint workflow instead of treating it as a pre-submission sprint catch vulnerabilities earlier, fix them cheaper, and pass reviews faster.
The FDA’s postmarket requirements aren’t going away. Building a culture where every developer understands why SBOMs exist and what vulnerability management means is more durable than any tool you deploy.
Here’s an uncomfortable truth we’ve observed working with fintech and e-commerce teams: most companies fail FDA cybersecurity reviews not because they lack technical skill, but because they misunderstand what regulators actually want. The FDA isn’t primarily looking for perfect security. It’s looking for defensible processes. Reviewers want to see that you know what’s in your software, that you have a plan when something goes wrong, and that you can prove it.
The checkbox mindset is short-sighted because it treats compliance as a finish line. In reality, it’s more like a maintenance contract. Companies that document proactively, update their plans consistently, and communicate transparently with regulators build a reputation that actually accelerates future clearances.
Understanding why security matters at an economic level, not just a technical one, is what separates leaders from laggards. The teams that outpace competition aren’t the ones with the most sophisticated security tools. They’re the ones whose documentation tells a clear, trustworthy story.
Navigating FDA cybersecurity requirements while running a fast-moving startup is genuinely hard. The documentation burden alone can overwhelm lean engineering teams, and a single gap in your SBOM or vulnerability plan can delay your entire product launch.
Testvox helps fintech and e-commerce teams close exactly these gaps. Our security testing services are built around FDA-aligned controls, OWASP standards, and practical documentation that holds up under scrutiny. Whether you need a full VAPT audit, SBOM generation support, or a review of your fintech app testing processes, we bring structured methodology without the enterprise overhead. You can see what a full FDA-ready security audit looks like in practice and decide if it fits your current stage.
Section 524B mandates transparent SBOMs, vulnerability management, and security controls for all cyber devices seeking market clearance. Without meeting these requirements, your product submission will be rejected before review even begins.
If your application manages or integrates with medical data, you may trigger FDA cybersecurity requirements even as an SME or startup. The key trigger is whether your software qualifies as a cyber device under the expanded FDA definition.
You risk blocked product launches, steep fines, legal liability, and reputational damage if found non-compliant with Section 524B controls. Enterprise partners and investors also frequently review compliance status as part of due diligence.
List all software components, including open-source libraries, and update the SBOM for every release or patch as required under FDA SBOM guidance. Tools like CycloneDX or SPDX-based platforms can automate much of this process.
Many teams use SCA tools, continuous monitoring apps, and automated testing solutions to maintain compliance and detect threats quickly, all of which align with FDA postmarket requirements. Snyk, Wazuh, and Burp Suite are commonly used across teams of all sizes.
Let us know what you’re looking for, and we’ll connect you with a Testvox expert who can offer more information about our solutions and answer any questions you might have?