UAE
Testvox FZCO
Fifth Floor 9WC Dubai Airport Freezone
Medical device cyberattacks are no longer a problem reserved for large hospital networks. 24% of healthcare organizations reported attacks on medical devices in 2026, with 80% of those incidents causing significant disruption to patient care and devices going offline for up to 12 hours. If you’re building a connected health product in India or the UAE, this is your threat landscape too. Penetration testing is the structured process that lets you find and fix security gaps before regulators, attackers, or patients pay the price. This guide covers the why, the how, and the costly mistakes to avoid.
| Point | Details |
|---|---|
| Testing is mandatory | Penetration testing is required for regulatory approval and patient safety. |
| Right method matters | White- or gray-box testing is essential; black-box alone is not enough for medical devices. |
| Avoid common pitfalls | Use production devices, include all interfaces, and always retest after updates. |
| Context shapes risk | Scoring must consider where and how devices are used, not just raw technical flaws. |
| Expert help simplifies compliance | Partnering with qualified providers keeps startups compliant and focused on innovation. |
The threat is real and growing. Malware infections, unauthorized network intrusions, and ransomware attacks are now routine events in healthcare environments. For a startup shipping a connected glucose monitor, a remote patient monitoring platform, or a smart infusion pump, the stakes are identical to those facing established hospital systems. A compromised device can delay treatment, corrupt readings, or expose sensitive patient data. The consequences are not just reputational.
Regulatory bodies have responded with firm requirements. The FDA mandates that penetration testing cover production-equivalent devices, meaning the exact hardware and software configuration you plan to ship, not a simplified prototype. The scope must include all system elements, every communication channel (Bluetooth, Wi-Fi, cellular, USB), and clearly defined security objectives. Submissions must document tester qualifications, the methodology used, and how each identified risk was resolved or accepted. India’s CDSCO is moving in the same direction as it aligns its medical device framework with international standards, and the UAE’s health authorities follow similar evidence-based approval requirements for software-driven devices.
Here is what the regulatory focus actually covers:
“The FDA’s expectation is not that your device is perfectly secure. The expectation is that you have systematically identified risks and made defensible decisions about each one. That is what an audit actually looks for.”
The rising rate of attacks on connected health devices means that regulators are not asking for penetration testing as a checkbox. They are asking for it because devices are actively being exploited, and patient harm is the documented result. Understanding medical device security standards at the start of your development cycle saves you from expensive late-stage redesigns.

With the “why” established, you need to understand how penetration testing is actually carried out for connected medical devices. The methodology you choose has a direct impact on what you find, what regulators accept, and how useful the results are for your engineering team.
There are three core approaches:
| Approach | Information given to tester | Best for medical devices? | Key limitation |
|---|---|---|---|
| White-box | Full access: source code, architecture, credentials | Yes, strongly preferred | Requires significant tester expertise |
| Gray-box | Partial access: some documentation, limited credentials | Yes, preferred | May miss some undocumented behaviors |
| Black-box | No prior information | Supplementary only | Misses software-hardware interactions |
The FDA flags black-box testing alone as insufficient for medical devices because it cannot reliably surface vulnerabilities in the interaction between software and hardware safety functions. A tester probing a cardiac monitor from the outside with no device knowledge will likely miss the firmware-level flaw that matters most. White- and gray-box testing are superior because they allow testers to trace attack paths through the actual system architecture, including proprietary protocols and safety-critical functions.
Here is how a complete penetration test actually runs, step by step:
Pro Tip: Choose a gray box strategy for your first full test. It balances depth with efficiency, gives testers enough context to find hardware-software interaction flaws, and produces documentation that satisfies regulatory reviewers. Supplement with targeted black-box testing for specific external interfaces if your submission requires it.
The white box approach is ideal for internal security reviews and pre-submission audits when your team wants maximum coverage. For a complete picture of your VAPT methods and how they apply to your specific device category, align your methodology choice with your regulatory pathway from day one.
Understanding the process is essential, but startups consistently trip over the same set of avoidable mistakes. These errors do not just slow down your submission. They can result in FDA holds, CDSCO audit failures, and in the worst case, a compromised device reaching patients.
The most common pitfalls include:
“A penetration test report is not a trophy. It is a living document that reflects your security posture at a specific point in time. Regulators know this, and they will check the date.”
Fixing security gaps identified during testing is only half the job. The other half is documenting that you fixed them and verifying through retesting that the fix held. Use your compliance checklist to track each finding through its full lifecycle: identified, assigned, fixed, retested, and closed.
Pro Tip: Build your penetration testing schedule around your firmware release cycle, not your regulatory submission deadline. Testing a device that is still changing is expensive and produces reports that are immediately outdated.
Finding vulnerabilities is only the first step. Accurately prioritizing them is where most startups struggle, and where the medical device context makes standard approaches inadequate.
The Common Vulnerability Scoring System (CVSS) is the industry standard for rating vulnerability severity. The base score rates factors like attack complexity, required privileges, and potential impact. It is a useful starting point. But CVSS Base alone misprioritizes vulnerabilities in medical contexts because it does not account for patient safety or deployment environment. A medium-severity network vulnerability in a hospital ICU monitor is categorically more dangerous than the same vulnerability in a fitness tracker used at home.
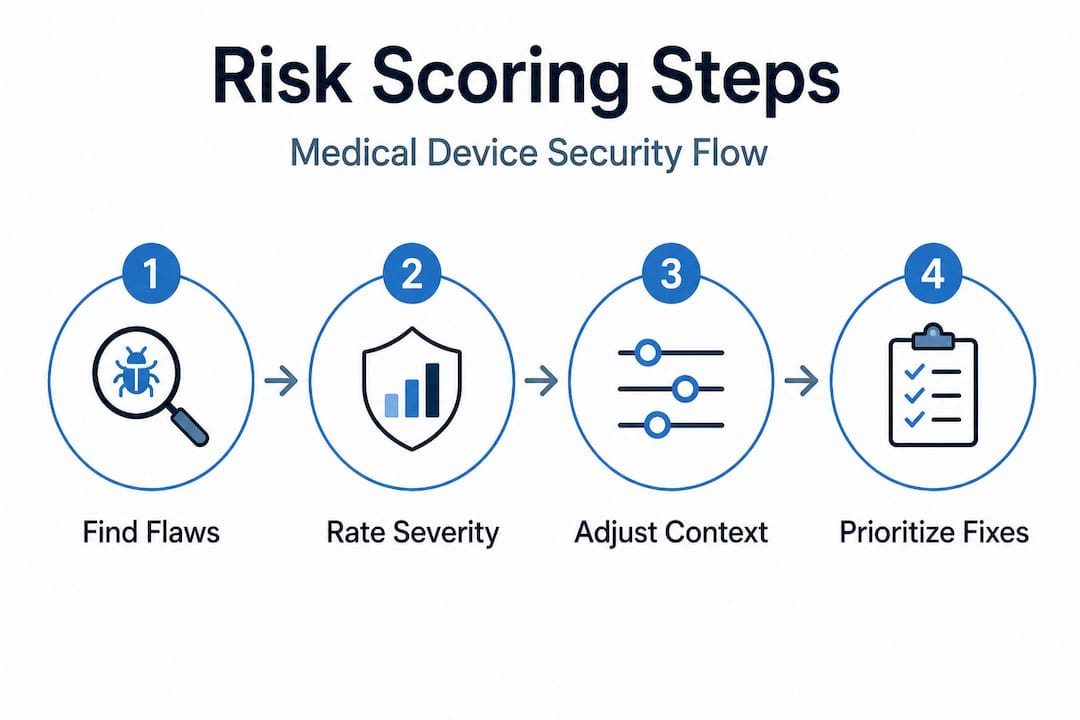
The BTE (Base, Temporal, Environmental) scoring model extends CVSS to address this gap. The environmental score adjusts for where and how the device is deployed, who has physical access, and what safety functions are at risk. The safety modifier adds weight for vulnerabilities that could directly affect patient treatment decisions or device behavior.
Here is a practical example of how context changes the risk picture:
| Vulnerability | CVSS Base | Hospital ICU deployment | Home use deployment |
|---|---|---|---|
| Unauthenticated Bluetooth pairing | 7.5 (High) | Critical: attacker could be in adjacent room | Moderate: limited attacker proximity |
| Unencrypted data transmission | 6.5 (Medium) | High: sensitive clinical data on hospital network | Low: consumer data, limited exposure |
| Default admin credentials | 8.1 (High) | Critical: network-connected, many users | High: single user, limited network access |
When evaluating your pen test provider, ask these specific questions about their risk scoring approach:
Full risk scoring that incorporates patient safety context is not optional for medical devices. It is what separates a compliance-grade report from a generic IT security assessment. For teams building IoT-device platforms that span hospital and home environments, this distinction is particularly important because the same device may carry very different risk profiles depending on where it is deployed.
Here is something most compliance guides will not tell you: perfect security is not achievable, and regulators know it. What the FDA, CDSCO, and UAE health authorities actually look for is evidence of a defensible, systematic process. They want to see that you identified risks, made informed decisions, and have a plan for ongoing assessment. That is a much more achievable target than “zero vulnerabilities.”
The startups we see struggle most with security compliance are not the ones with the most vulnerabilities. They are the ones who either did nothing or tried to build an enterprise-grade security program on a seed-stage budget and ran out of time before their submission. Both extremes fail.
The practical path looks like this: start with a scoped, context-aware penetration test on your production-equivalent device as early as possible in your development cycle. Use the findings to prioritize your engineering backlog, not to panic. Fix the critical and high findings, document your reasoning for accepting lower-risk items, and retest before submission. Then build a lightweight process for reassessing when the device changes or the deployment context shifts.
One insight that often surprises founders: the patient-facing context of your device matters more than its technical complexity. A simple Bluetooth-connected thermometer deployed in a neonatal ICU carries more regulatory scrutiny than a sophisticated remote monitoring platform used by healthy adults. Reassess your risk scoring every time the clinical context changes, not just when you add new features.
Invest in the most context-aware risk scoring you can afford, but do not overbuild controls for risks that your deployment environment does not actually present. A device used only on a private clinical network does not need the same hardening as one that connects directly to consumer smartphones over public Wi-Fi. Lean on medical security testing realities from partners who have navigated these submissions before. The goal is audit-proof practice, not theoretical perfection.
Navigating FDA, CDSCO, and UAE health authority requirements for medical device security is genuinely complex, and the cost of getting it wrong is measured in delayed approvals and compromised patient safety. Testvox works directly with healthtech startups in India and the UAE to deliver penetration testing and VAPT services built for regulatory submissions.
Our security testing services are designed around the specific documentation and methodology requirements that medical device regulators expect. We have hands-on experience with medical device security scenarios, including production-equivalent device testing, BTE risk scoring, and the retest cycles that turn findings into closed compliance items. Whether you need a one-time pre-submission audit or an ongoing security partner, our penetration testing and VAPT team can help you get there without overbuilding or overspending. Talk to us before your next firmware release.
Yes. The FDA requires penetration testing on production-equivalent devices as part of cybersecurity documentation, and both CDSCO and UAE health authorities require security evidence for networked or software-driven medical device approvals.
White- or gray-box testing is strongly recommended because black-box approaches alone miss critical software-hardware interactions and safety function vulnerabilities that regulators specifically look for.
Reports older than one year are considered stale by regulators and can cause FDA holds or CDSCO audit failures; retesting is also required after any significant fix or device change.
No. CVSS Base alone misprioritizes medical device risks because it ignores patient safety context and deployment environment; a vulnerability in a hospital ICU device carries far greater weight than the same flaw in a consumer wellness product.
Let us know what you’re looking for, and we’ll connect you with a Testvox expert who can offer more information about our solutions and answer any questions you might have?