UAE
Testvox FZCO
Fifth Floor 9WC Dubai Airport Freezone
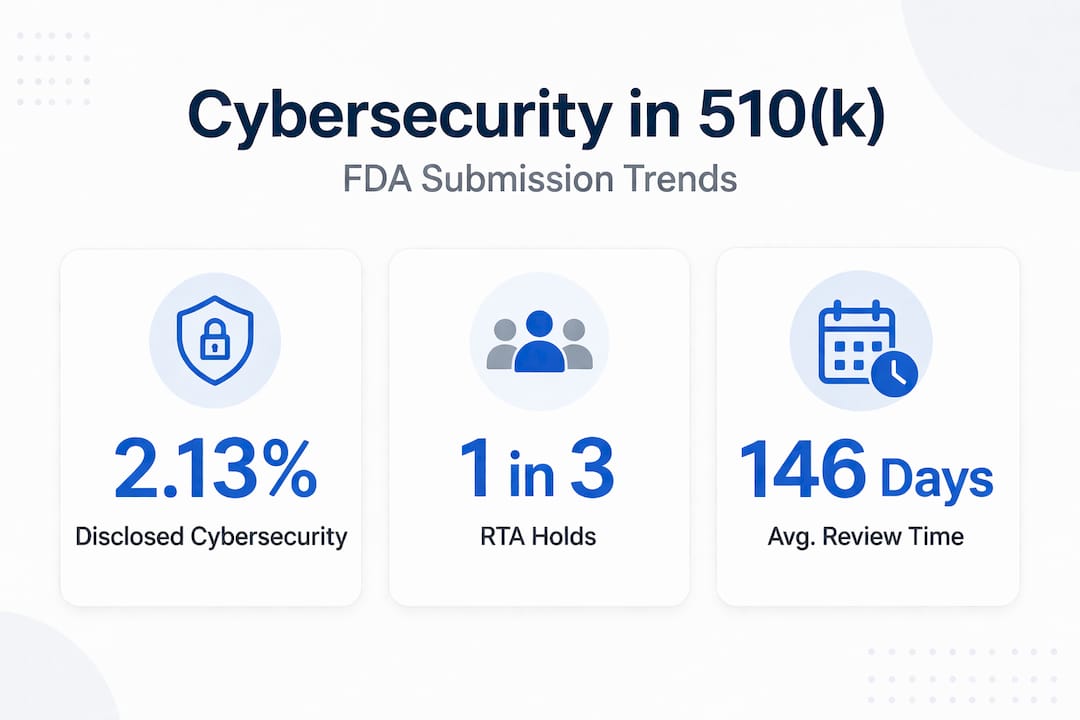
Roughly one in three 510(k) submissions hits a Refuse to Accept hold before a single substantive review even begins, and cybersecurity deficiencies rank among the most cited reasons. With an average review timeline already stretching to 146 to 147 days in 2025, a preventable security documentation gap can push your launch back by months and burn through capital you cannot afford to lose. This guide breaks down exactly what the FDA expects from a cybersecurity standpoint, how to build security into your device from the start, and the practical steps Indian and US founders need to take to reach clearance without unnecessary detours.
| Point | Details |
|---|---|
| Cybersecurity is essential | Weak or missing security evidence is a top reason for 510(k) delays and rejections. |
| Early integration saves time | Building security into the device from the start streamlines compliance and reduces risk. |
| FDA documentation is specific | Successful submissions include designated threat models, test reports, and SBDF/SPDF content. |
| Post-2023 enforcement is stricter | Modern submissions face more rigorous FDA scrutiny than ever before—compliance can’t be an afterthought. |
| Expert guidance accelerates success | Leveraging domain specialists can help startups avoid costly delays and build trust with regulators. |
The FDA’s posture on cybersecurity has shifted from gentle guidance to hard enforcement. Before 2023, reviewers might flag a missing threat model as a minor deficiency. Today, the same gap can freeze your entire submission. If your device qualifies as a “cyber device,” you are legally required to meet a specific set of security documentation standards before the FDA will even begin substantive review.
FDA premarket cybersecurity guidance requires specific cybersecurity documentation in 510(k) submissions for all devices with cybersecurity risks, including cyber devices under Section 524B of the FD&C Act. This is not optional language buried in a footnote. It is a statutory requirement that took effect with the Consolidated Appropriations Act of 2023.
So what exactly is a cyber device? The FDA’s definition is precise:
A cyber device is one that includes software validated by the sponsor, has the ability to connect to the internet, and contains features or functions that could be vulnerable to cybersecurity threats.
Cyber devices are defined as devices that include software validated by the sponsor, can connect to the internet, and have characteristics vulnerable to cybersecurity threats. That definition covers a surprisingly wide range of products: wearable cardiac monitors, connected glucose meters, hospital infusion pumps with remote dosing features, and even diagnostic imaging software with cloud upload capability.
Two dangerous misconceptions still circulate in startup circles:
Founders who learn this lesson late often discover it when they receive an RTA hold letter, at which point they face a complete documentation rebuild under time pressure. Understanding FDA cybersecurity requirements before you start building is the single highest-leverage move you can make early in development.
Now that we know security is essential, let’s break down what documentation you need to deliver and avoid getting stuck in review holds.
The FDA does not leave you guessing about what to submit. The eSTAR (Electronic Submission Template and Resource) format includes a dedicated cybersecurity section, and reviewers use a structured checklist to evaluate it. Missing or thin documentation in this section is a primary trigger for Additional Information requests. Missing cybersecurity docs can lead to AI requests in roughly 67% of affected cases, which adds weeks or months to your timeline.
Here is a comparison of what pre-2025 submissions often included versus what the FDA now expects:
| Documentation component | Pre-2025 common practice | 2025 to 2026 FDA expectation |
|---|---|---|
| Threat model | Often absent or informal | Formal STRIDE or equivalent, mapped to device architecture |
| SBDF/SPDF | Rarely included | Required for cyber devices; must cover full lifecycle |
| Risk assessment | Generic software risk table | Device-specific, tied to threat model findings |
| Penetration test evidence | Almost never submitted | Expected for high-risk connectivity features |
| QMSR/ISO 13485 alignment | Loosely referenced | Explicit mapping to cybersecurity controls required |
| eSTAR cybersecurity section | Not applicable | Mandatory structured section with all components |
The FDA premarket cybersecurity guidance is explicit: every submission for a cyber device must include documented evidence of security controls, not just assertions that controls exist.
To build a complete cybersecurity documentation packet, follow these steps:
Following these compliance steps systematically is far less painful than trying to reconstruct documentation after an RTA hold.
Once documentation needs are clear, let’s make sure your security strategy is robust from day one with actionable steps.

The most expensive security mistake a startup can make is treating cybersecurity as a documentation exercise rather than an engineering discipline. Founders who integrate security into their development process from the first sprint consistently produce better submissions and face fewer review holds. The reason is simple: FDA reviewers can tell the difference between a threat model that shaped design decisions and one that was reverse-engineered from a finished product.
Early SBDF/SPDF integration and gap analysis against 2025 FDA guidance are the two highest-impact early investments for startups in both India and the US. A gap analysis compares your current security posture against the specific requirements in the FDA’s latest cybersecurity guidance and the eSTAR template. It tells you exactly where you are exposed before a reviewer does.
Core activities your engineering team should build into every development cycle:
Pro Tip: The single most common gap we see in startup submissions is a threat model that covers the device in isolation but ignores the broader ecosystem: the mobile app, the cloud backend, the clinical workflow. FDA reviewers evaluate the full attack surface. Make sure your threat model does too. A good penetration testing guide can help you scope this correctly before testing begins.
Fixing security gaps early in development costs a fraction of what it costs to fix them after a submission hold. One startup we worked with spent three months rebuilding their threat model after an RTA. The same work done at the design stage would have taken three weeks.
After developing a sound security strategy, it’s key to understand how the regulatory and compliance environment has evolved and why startups must avoid old patterns.
The historical data on cybersecurity disclosure in 510(k) submissions is striking. Only 2.13% of software-containing devices submitted between 2002 and 2016 mentioned cybersecurity in their summaries, rising to just 5.5% in 2015 to 2016. That means the overwhelming majority of connected medical devices reached the market with essentially no documented security posture.
| Period | Devices with software | Cybersecurity mentioned | Disclosure rate |
|---|---|---|---|
| 2002 to 2010 | High volume | Very rare | Under 1% |
| 2011 to 2014 | Growing | Occasional | ~1.5% |
| 2015 to 2016 | Significant | Increasing | ~5.5% |
| 2023 to 2026 | Majority | Required by law | 100% expected |
Post-2023 enforcement has risen sharply with QMSR and ISO 13485 alignment now embedded in FDA expectations. The agency is not simply asking for more paperwork. It is requiring evidence that security is a core engineering discipline within your quality management system.
“The FDA’s shift from voluntary guidance to statutory enforcement represents the most significant change in 510(k) requirements in a generation. Startups that treat this as a paperwork update rather than a fundamental change in how devices must be built will face repeated submission failures.”
Why does this matter beyond the submission itself? Because the FDA now evaluates your ability to support the device post-market. A weak security posture at submission signals to reviewers that your organization lacks the processes to respond to vulnerabilities discovered after clearance. That concern can delay or derail approval even when your clinical evidence is strong.
Startups that want to avoid common cybersecurity mistakes need to understand that the old playbook of submitting minimal documentation and responding to deficiencies reactively no longer works. The FDA has the statutory authority to refuse submissions outright, and it is using it.
Here is an uncomfortable truth from working with dozens of device startups: most founders know security matters, but they consistently underestimate how much evidence the FDA wants to see that security shaped the product, not just the submission.
The pattern repeats itself. A team builds a genuinely innovative device, runs a tight development schedule, and then allocates the final four to six weeks before submission to “handle the cybersecurity documentation.” What follows is a frantic effort to produce a threat model, risk assessment, and test reports that look credible but were never connected to actual design decisions. Reviewers are experienced enough to spot this. The documents may be technically complete but internally inconsistent, and that inconsistency triggers an AI request.
The deeper problem is that many founders treat FDA cybersecurity requirements as a compliance tax rather than a quality signal. The FDA’s requirements exist because insecure medical devices cause real patient harm. A compromised insulin pump or a manipulated cardiac monitor is not a data breach. It is a clinical event. When you internalize that framing, the documentation requirements stop feeling arbitrary and start feeling proportionate.
What separates timely approvals from costly delays is almost always the same thing: teams that integrated real-world compliance steps into their engineering sprints versus teams that tried to produce compliance artifacts after the fact. The former group submits with confidence. The latter group submits and waits for the hold letter.
Pro Tip: Assign a cybersecurity owner within your engineering team at the start of the project, not the start of the submission process. This person owns the threat model, tracks SBDF updates as dependencies change, and ensures every sprint review includes a security checkpoint. This single structural decision prevents the majority of documentation gaps we see in startup submissions.
Getting your 510(k) cybersecurity documentation right the first time requires more than good intentions. It requires structured testing, documented evidence, and a team that understands what FDA reviewers actually look for.
Testvox specializes in exactly this kind of work. Our security testing service is built for medical device startups navigating FDA submission requirements, covering threat modeling support, VAPT aligned with OWASP standards, and test report documentation formatted for regulatory review. We have helped device teams produce submission-ready security packages that hold up under FDA scrutiny. If you want to see what this looks like in practice, our security compliance case study walks through a real patient monitoring device we helped clear. Start your submission on solid ground.
FDA premarket cybersecurity guidance requires threat modeling, SBDF/SPDF, risk analysis, security test reports, and a completed cybersecurity section within the eSTAR template for all cyber devices.
Average review time runs about 146 to 147 days, but missing cybersecurity documentation can trigger an Additional Information request that pauses the clock entirely and extends your timeline by months.
A cyber device includes validated software, internet connectivity, and features susceptible to cybersecurity threats, covering most modern connected medical devices regardless of their size or complexity.
Your 510(k) can be placed on RTA hold or receive an AI request, and missing cybersecurity docs trigger these outcomes in roughly 67% of affected submissions, causing significant approval delays.
FDA expectations are identical for all submissions regardless of where the company is based. Both Indian and US startups must meet the same QMSR alignment and cybersecurity documentation standards that apply to any 510(k) submission for a cyber device.
Let us know what you’re looking for, and we’ll connect you with a Testvox expert who can offer more information about our solutions and answer any questions you might have?