UAE
Testvox FZCO
Fifth Floor 9WC Dubai Airport Freezone

 14 May 2026
14 May 2026
 10 min 60 sec
10 min 60 sec
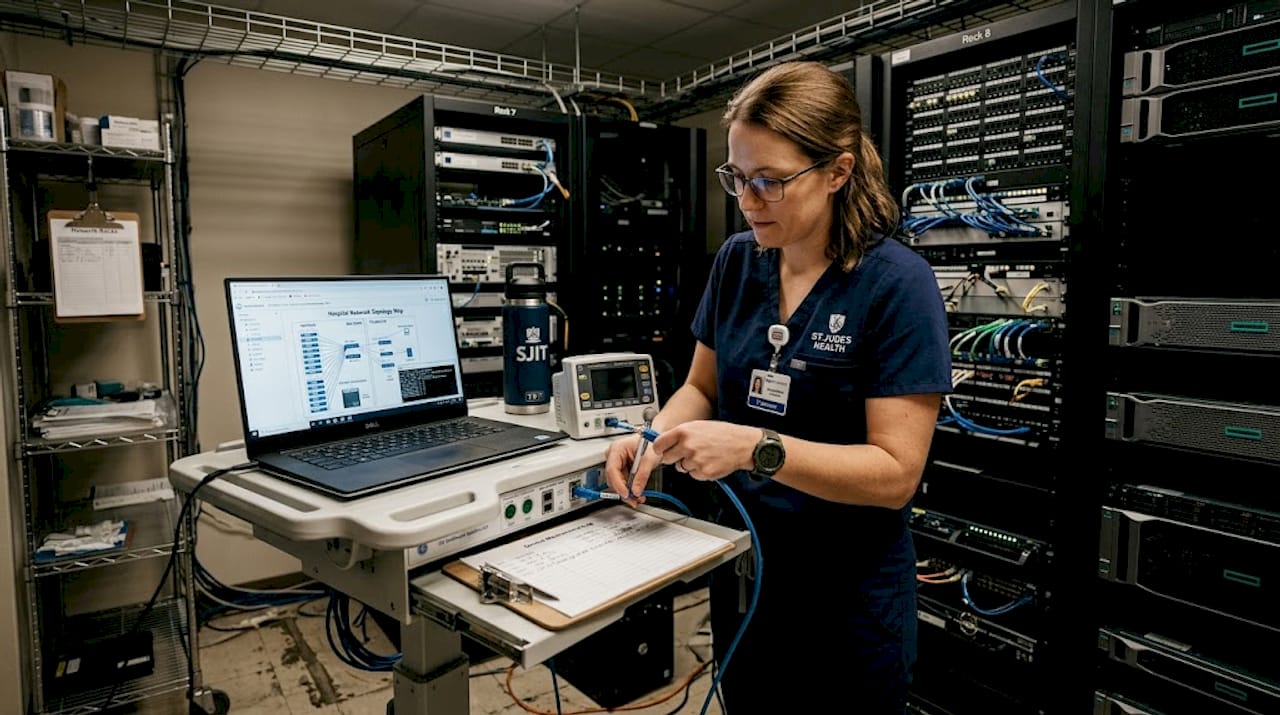
Medical device companies in India and the UAE are operating in a threat environment far more hostile than most CTOs realize. Connected device attacks are not occasional events but a continuous, high-volume reality that demands defensible, repeatable security testing evidence. Running a single penetration test before launch is no longer enough. Regulators expect structured, lifecycle-based programs that produce traceable artifacts, and the standards and frameworks to build those programs already exist. This article shows you exactly how to construct one.
| Point | Details |
|---|---|
| Lifecycle testing is essential | Security testing must verify implemented controls across the device lifecycle, not just at single points. |
| Use recognized standards | Adopting standards like AAMI TIR 57 and IEEE 2621 makes programs defensible and reproducible for regulators. |
| Prioritize using contextual risk scores | CVSS v4.0 BTE scoring helps focus remediation efforts on risks that matter most for patient safety and compliance. |
| Test the ecosystem, not just devices | Edge-case vulnerabilities often arise from device interactions and app/data flows, not just internal code. |
| Defensible evidence drives compliance | Repeatable, structured testing results are key for market access and ongoing regulatory approval. |
Security testing for medical devices is fundamentally different from testing a mobile app or a web platform. Regulators do not accept a one-time vulnerability report as proof that your device is safe. They want evidence that security is managed continuously, across the full device lifecycle, with documented controls that can be reviewed, audited, and defended.
The FDA is the clearest example. FDA cybersecurity expectations require Quality System (QS) considerations baked into every stage of product development, plus specific content in premarket submissions covering identified security risks, the controls you implemented, and the testing artifacts that verify those controls work. That is not a checklist item you tick before submission. It is an ongoing obligation that extends into postmarket surveillance and structured vulnerability management.
For companies targeting the Indian market, the picture is shaped by different but equally demanding requirements. BIS certification and CDSCO registration require compliance evidence aligned with Indian Standards (IS) and established testing processes. Understanding what documentation must be produced, and in what format, is critical to avoiding costly re-submissions. The medical device market compliance landscape in India is evolving rapidly, with increasing alignment to international standards.
For UAE-based companies, the Health Authority Abu Dhabi (HAAD) and Dubai Health Authority (DHA) both reference international standards in their device registration frameworks. Building your security testing program around globally recognized standards is the most reliable way to satisfy multiple regulators simultaneously.
A critical insight: Regulatory agencies are not asking whether you found vulnerabilities. They are asking whether your organization has a structured process for identifying, evaluating, and mitigating security risks on an ongoing basis. The testing artifacts are evidence of that process.
Learning about FDA cybersecurity requirements early in your product roadmap will save you significant rework costs later. And if you are preparing a 510(k) submission, understanding the FDA 510(k) security strategy requirements before you start testing is essential.
Good security hygiene also extends beyond regulatory compliance. Applying cybersecurity best practices at every development stage reduces the gap between what regulators expect and what your product actually delivers.
Once you understand what regulators expect, the next question is: what frameworks should guide how you test? The answer matters because standards-based testing produces reproducible results that map directly to submission evidence. Ad hoc testing does not.
Medical device security testing should be grounded in recognized security standards and lifecycle risk management, not just standalone penetration testing.
| Standard | Primary focus | What it adds to your program |
|---|---|---|
| AAMI TIR 57 | Security risk management | Lifecycle risk framework, threat modeling guidance |
| IEC 81001-5-1 | Health software security | Software-specific security activities across SDLC |
| UL 2900-2-1 | Network-connectable devices | Structured penetration testing and risk scoring |
| IEEE 2621 | Standardized evaluation | Reproducible test plans and checklists for evidence mapping |
IEEE 2621 is particularly valuable because it provides a standardized evaluation approach using structured test plan checklists that align with other lifecycle and risk management guidance. This means your test results can be directly mapped to regulatory submission requirements. That traceability is what turns a vulnerability scan into defensible evidence.
How do these standards work together in practice? Think of AAMI TIR 57 as your risk management spine. It defines how you identify threats, score risks, and decide which controls to implement. IEC 81001-5-1 then specifies the security activities your software development process must include. UL 2900-2-1 drives your actual penetration testing protocol. And IEEE 2621 gives you the structured evaluation checklists that tie everything together into a submittable evidence package.
Engaging with Notified Body cybersecurity requirements early is critical if you are targeting European CE marking alongside FDA or CDSCO registration. The security risk assessment methodology you choose should produce outputs that satisfy all of these bodies simultaneously.
Document your test plans in a format that maps each test case to the specific security control it validates and to the regulatory requirement that control satisfies. This three-way traceability matrix is the single most effective tool for accelerating regulatory submissions and responding to reviewer questions.
For a deeper look at how these standards interact in a real product context, the complete guide to medical device security walks through a practical implementation scenario.
Finding vulnerabilities is the easy part. Deciding which ones to fix first, given limited engineering time and a looming regulatory submission deadline, is where most teams struggle. Standard CVSS base scores give you a number, but they do not tell you how dangerous a vulnerability actually is in your specific deployment environment.
CVSS v4.0 BTE (Base, Threat, Environmental) scoring can substantially change vulnerability prioritization compared to relying only on base scores. A vulnerability rated Critical in the base metric might drop to Medium when you factor in that it requires physical device access in a controlled clinical setting. Conversely, a High-rated vulnerability might become Critical when your device is deployed in home care environments where network controls are minimal.
| Vulnerability | CVSS base score | Hospital BTE score | Home care BTE score |
|---|---|---|---|
| Unencrypted BLE pairing | 7.5 High | 5.2 Medium | 8.9 Critical |
| Default admin credentials | 9.1 Critical | 9.1 Critical | 9.1 Critical |
| Outdated TLS library | 6.5 Medium | 4.8 Medium | 7.2 High |
| Unauthenticated API endpoint | 8.2 High | 7.0 High | 9.0 Critical |
A structured prioritization approach using contextual scoring looks like this:
The risk assessment best practices that work for software-only products need significant adaptation for devices where a security failure can directly affect patient safety. Contextual scoring is the bridge between a vulnerability list and a safety-aware remediation plan.
Here is a misconception that catches even experienced CTOs: most vulnerabilities in modern connected medical devices do not live in the device firmware. They live in the interactions between the device, its companion app, the cloud backend, the pairing protocol, and the clinical network it connects to.
Ecosystem-level weaknesses in BLE and MIoT implementations discovered through threat-model-guided penetration testing represent some of the most critical exposures in medical device security programs. These are precisely the vulnerabilities that a device-only penetration test will miss entirely.
The volume of attacks against connected medical device protocols is continuous and severe. Attack volume against connected device protocols is extremely high, which means that weaknesses in any part of your device ecosystem will be discovered and exploited by adversaries.
Pro Tip: Build a threat model that maps every data flow and trust boundary in your device ecosystem before you write a single test case. The areas where trust assumptions change (device to app, app to cloud, cloud to clinical system) are exactly where your most serious vulnerabilities will be found.
Understanding comprehensive penetration testing strategies for medical devices requires thinking beyond firmware analysis. Your penetration testing compliance plan should explicitly document which ecosystem interactions were tested and what evidence was generated for each.
The threat intelligence around medical devices is not theoretical. Healthcare environments face one attack every 20 seconds targeting DICOM protocols, with nearly 1 million vulnerabilities identified across hundreds of vendors and over 99% of healthcare organizations affected. Your testing program must reflect this reality.
“Healthcare environments experience attacks against DICOM protocols at a rate of one every 20 seconds, with nearly 1 million vulnerabilities from hundreds of vendors affecting more than 99% of organizations.” Source: Censinet
What does this mean for how you design and execute tests? Several things:
The evidence defensibility in VAPT context matters enormously here. A penetration test that produces a PDF report is useful for development teams. A structured testing program that produces traceable, reproducible artifacts is what regulators and enterprise customers demand. Good data center security best practices provide a useful parallel for understanding how to design monitoring and detection systems that complement your device security testing.
Most CTOs we speak with treat security testing as an event. Something you schedule before a major release, complete in a few weeks, and then move on from. That mental model made sense ten years ago. It does not reflect what regulators, enterprise customers, or the threat landscape demand in 2026.
Treating security testing as lifecycle verification of implemented security risk controls, rather than a periodic penetration test, is the foundation of a mature medical device security program. The distinction sounds subtle but the operational difference is significant.
Lifecycle verification means that every time you make a software change, update a third-party component, or modify a network interface, you rerun the relevant security tests and regenerate the traceability evidence. It means your risk register is a living document, not a snapshot. It means your security testing team works in parallel with your development team, not as a final gate before submission.

The traceability requirement is the piece most CTOs underestimate. Regulators reviewing your submission do not just want to know that you found vulnerabilities and fixed them. They want to trace a specific threat, through your risk analysis, to the control you implemented, through to the test that verified the control works, and through to the postmarket process that will catch it if the control degrades over time. Building that chain of evidence from the start is dramatically cheaper than reconstructing it under regulatory review pressure.
Another overlooked area: many teams build technically excellent security testing programs but fail to align those programs with their QMS (Quality Management System) documentation. Every test artifact must be version-controlled, linked to the product version it applies to, and accessible under your QMS. Otherwise, even a technically strong testing program produces evidence that is hard to defend.
For companies ready to ace their cybersecurity assessment, the shift from event-based to lifecycle-based testing is the single highest-leverage change available. It reduces regulatory risk, improves product quality, and builds the kind of security posture that enterprise healthcare customers and partners increasingly require before signing contracts.
Building a lifecycle-based security testing program from scratch is a significant investment. You need deep expertise in medical device standards, regulatory requirements across multiple jurisdictions, threat modeling methodologies, and penetration testing execution. Most medical device startups and SMEs do not have all of that in-house, and they should not need to.
Testvox provides expert security testing services tailored specifically for medical device companies in India and the UAE. Our team has worked through real compliance scenarios like the FDA-ready patient monitoring device case study, where we built a complete standards-based testing program from threat modeling through submission artifacts. We have also delivered structured security testing for complex compliance management systems where evidence traceability was the primary requirement. Whether you need a full lifecycle security testing program, VAPT aligned to OWASP and recognized device standards, or a pre-submission security audit, Testvox brings the domain expertise to get you across the regulatory finish line with confidence.
Standards such as AAMI TIR 57, IEC 81001-5-1, UL 2900-2-1, and IEEE 2621 are widely recognized, with UL guidance emphasizing that testing must go beyond standalone penetration tests to include lifecycle risk management.
Security testing evidence must satisfy BIS certification and CDSCO requirements by demonstrating compliance with Indian Standards and documenting that safety and security testing was conducted according to recognized processes.
Because CVSS v4.0 BTE scoring can substantially shift how a vulnerability is rated when you factor in deployment environment, patient population, and realistic threat context, leading to much safer and more cost-effective remediation decisions.
Ecosystem-level vulnerabilities emerge from interactions between devices, companion apps, cloud backends, and clinical networks. BLE and MIoT ecosystem weaknesses discovered via threat-model-guided testing represent exposures that device-only testing will miss entirely.
Using IEEE 2621 test plan checklists aligned with lifecycle risk management frameworks ensures every test result is reproducible, traceable to specific controls, and formatted to satisfy regulatory reviewer expectations.
Let us know what you’re looking for, and we’ll connect you with a Testvox expert who can offer more information about our solutions and answer any questions you might have?