UAE
Testvox FZCO
Fifth Floor 9WC Dubai Airport Freezone
Passing an FDA premarket submission does not mean your device is secure. Attackers do not care about your compliance documentation. They probe firmware, exploit insecure update channels, and pivot from a connected infusion pump to an entire hospital network. Ransomware attacks on healthcare have made it clear that regulatory approval and genuine security are two different things. This guide cuts through the noise and gives CTOs and founders a practical, framework-driven approach to security risk assessment that protects patients, satisfies regulators, and builds lasting trust.
| Point | Details |
|---|---|
| Exploitability is key | Modern risk assessments prioritize how easily vulnerabilities can be exploited, not just their likelihood. |
| Context matters | Hospital and home environments change risk scores and mitigation priorities dramatically. |
| Frameworks drive results | Combining SPDF, STRIDE, and CVSS creates a comprehensive approach to device security. |
| Continual maturity | Adopting benchmarks and leadership roles ensures security is maintained and improved postmarket. |
| Beyond compliance | True device security requires active testing, culture change, and anticipating real-world threats. |
The stakes in medical device security are unlike anything in conventional software development. A misconfigured authentication module in a fintech app might expose transaction data. The same flaw in a cardiac monitor could cost a patient their life. That asymmetry changes everything about how you must think about risk.
Regulatory bodies have caught up to this reality. The FDA now requires manufacturers to submit a cybersecurity risk assessment as part of premarket submissions, and the EU Medical Device Regulation (EU MDR) mandates security considerations throughout the entire product lifecycle. These are not optional add-ons. They are hard requirements that can block your device from reaching the market.
The threat landscape is equally demanding. Ransomware groups specifically target hospital networks because the pressure to restore operations is enormous, which means they pay. Insecure cloud connectivity in wearable patient monitors creates pathways for data theft and device manipulation. Legacy protocols like Bluetooth Low Energy, when poorly implemented, expose devices to replay attacks and man-in-the-middle exploits.
Here is what makes medical device security risk assessment fundamentally different from a standard software audit:
Following the cybersecurity compliance steps required by regulators is a starting point, not a finish line.
“Security risk assessment in medical devices is not about eliminating all risk. It is about understanding which risks are exploitable, tracing them to patient harm, and demonstrating that your mitigations are proportionate and documented.”
Three frameworks form the backbone of any credible medical device security risk assessment program. Understanding them individually is useful. Knowing how they interact is essential.
The Secure Product Development Framework (SPDF) is the FDA’s preferred lifecycle model. It requires security to be built into every stage of product development, from initial design through decommissioning. SPDF is not a single tool. It is an organizational commitment to secure-by-design principles. Teams that adopt SPDF integrate threat modeling early, conduct security architecture reviews before coding begins, and plan for vulnerability disclosure before launch.
STRIDE is a threat modeling methodology that categorizes threats into six types: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege. When you apply STRIDE to a medical device, you systematically ask: can an attacker impersonate a legitimate user? Can they alter data in transit? Can they deny that a transaction occurred? This structured questioning surfaces threats that ad hoc reviews consistently miss. The STRIDE threat model combined with CVSS scoring and an exploitability matrix gives teams a repeatable, auditable process.
CVSS v4.0 introduces a Base, Threat, and Environmental (BTE) scoring model that is a significant upgrade over earlier versions. Base scores reflect intrinsic vulnerability severity. Threat scores adjust for current real-world exploit availability. Environmental scores factor in your specific deployment context, such as whether the device operates in a controlled ICU or in a patient’s home. A vulnerability that scores 6.5 in a hospital environment might score 8.8 in a home setting because the compensating controls present in a clinical facility simply do not exist at home.
| Framework | Primary function | When to apply |
|---|---|---|
| SPDF | Lifecycle security governance | From design through decommission |
| STRIDE | Threat identification and categorization | During architecture and design phases |
| CVSS v4.0 BTE | Context-driven vulnerability scoring | During assessment and post-mitigation re-scoring |
Pro Tip: Do not apply STRIDE as a one-time exercise. Revisit your threat model every time you add a new interface, change a communication protocol, or update firmware. Attackers evolve. Your threat model should too.
Consulting a penetration testing guide tailored to medical devices will show you how these frameworks translate into actual test cases. If you are early in your compliance journey, the startup compliance guide provides a practical roadmap for resource-constrained teams.
Theory without process is just vocabulary. Here is how a rigorous security risk assessment actually unfolds for a connected medical device.
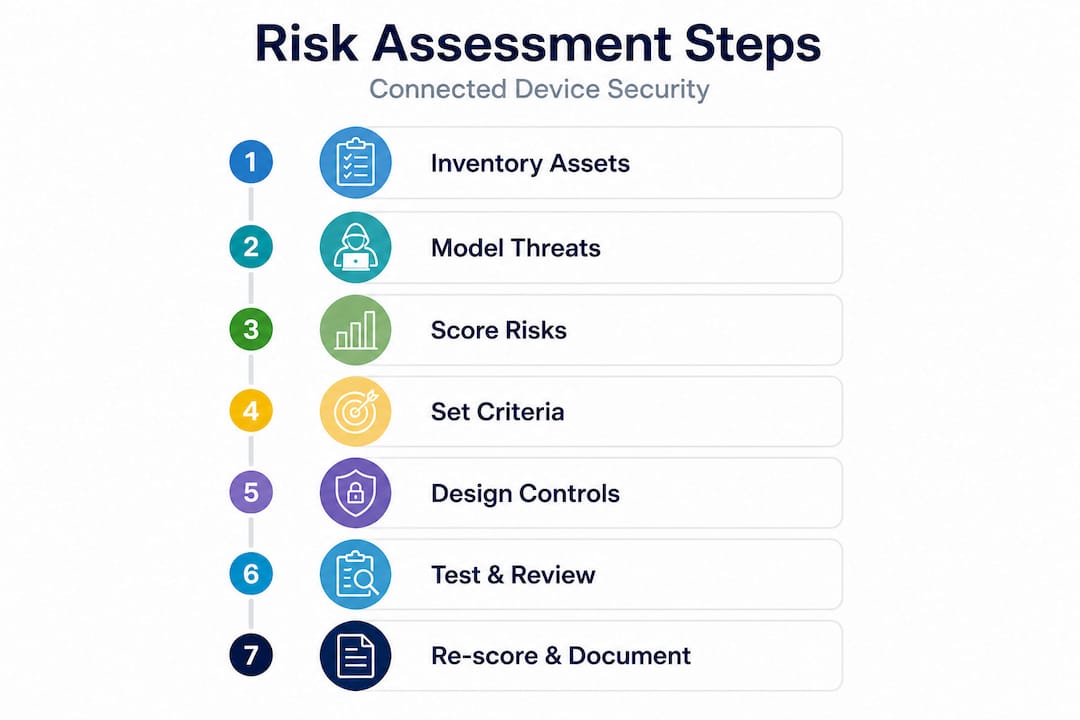
1. Build your asset inventory and map the environment. List every hardware component, software module, communication interface, and data flow. Map the physical environments where the device will operate. A device used only in hospitals faces different threats than one deployed in ambulances or homes.
2. Apply STRIDE to each asset and interface. For every asset, work through all six STRIDE categories. Document each identified threat with a description, the affected asset, and the potential patient safety impact. This step often surfaces 40 to 60 distinct threats for a moderately complex device.
3. Score each threat using CVSS v4.0 BTE. Start with the Base score, then layer in Threat intelligence from sources like the National Vulnerability Database (NVD). Finally, apply your Environmental score based on deployment context. The formula is straightforward: Risk equals exploitability multiplied by severity of harm, tracked via CVSS v4.0 and NVD data.
4. Define your risk acceptance criteria before you start mitigating. This is a step many teams skip, and it creates problems later. Decide in advance which CVSS score thresholds require immediate remediation, which require compensating controls, and which are acceptable with documentation. This prevents scope creep and keeps your risk register auditable.
5. Design and implement security controls. Controls fall into several categories: strong authentication and access control, data encryption in transit and at rest, secure over-the-air update protocols, audit logging, and network segmentation. The FDA guidance explicitly lists authentication, encryption, and penetration and fuzzing testing as key elements of a complete security program.
6. Test your controls with penetration testing and fuzzing. Penetration testing validates that your controls work as designed. Fuzzing sends malformed or unexpected inputs to interfaces to find crashes, memory corruption, and unexpected behavior. Both are required for credible FDA submissions.
7. Re-score after mitigations and document residual risk. Every mitigated threat gets a new CVSS BTE score. Residual risks that exceed your acceptance threshold require escalation or redesign.
| Assessment stage | Key output | Regulatory relevance |
|---|---|---|
| Asset inventory | Threat surface map | FDA premarket submission |
| STRIDE analysis | Threat register | EU MDR Annex I |
| CVSS BTE scoring | Risk prioritization matrix | FDA cybersecurity bill of materials |
| Control implementation | Security architecture document | Both FDA and EU MDR |
| Post-mitigation scoring | Residual risk register | Postmarket surveillance plan |
Following structured device compliance steps ensures your documentation maps cleanly to regulatory expectations. For teams discovering gaps mid-process, guidance on fixing cybersecurity gaps can accelerate remediation without derailing your timeline.
Even teams that follow the frameworks correctly can stumble on edge cases that regulators and attackers both notice.
Cascading threats across layers. Modern connected medical devices span physical hardware, local network, cloud services, and mobile companion apps. An attacker rarely attacks just one layer. They compromise a Bluetooth interface to gain network access, then pivot to a cloud API to exfiltrate data or alter device settings. Cross-layer cascading threats in connected medical device infrastructure are a documented risk that single-layer assessments miss entirely.

Home versus hospital deployment. This is one of the most underappreciated variables in medical device security. Hospital environments include network segmentation, IT security teams, physical access controls, and monitored infrastructure. Home environments have none of these. Research shows that home deployment scores can run up to 2.3 CVSS points higher than hospital scores for the same vulnerability. If your device is cleared for home use, your risk assessment must reflect that context explicitly.
Conflating safety and security. Safety risk management (ISO 14971) and security risk management address related but distinct concerns. Safety focuses on unintentional failure modes. Security focuses on intentional exploitation. The FDA is explicit that security risks are distinct from safety risks and must be assessed with exploitability as the primary driver, not probability. Teams that check security boxes inside their safety risk file often miss adversarial scenarios entirely.
Common mistakes that appear repeatedly in FDA feedback letters include:
Pro Tip: Build your risk assessment in a living document system, not a static PDF. Every change to device architecture, software version, or deployment environment should trigger a review of affected threat model entries. Static documents become liabilities the moment the device changes.
Staying current on security trends for CTOs helps you anticipate emerging threat categories before they appear in your next FDA interaction.
A single well-executed risk assessment is valuable. A repeatable, improving security program is a competitive advantage.
Maturity frameworks give you a roadmap. The Medical Device Innovation Consortium (MDIC) publishes benchmark data showing that organizations using maturity frameworks or with a dedicated Chief Product Security Officer demonstrate measurably higher maturity across all cybersecurity domains. MDIC’s Total Product Lifecycle (TPLC) benchmarks let you compare your program against industry peers and identify specific gaps.
The Chief Product Security Officer role is becoming standard at serious health tech companies. This person owns the security risk management program, drives cross-functional accountability, and serves as the primary liaison with regulators on cybersecurity matters. Without this ownership, security tends to fall between engineering and compliance without either team fully responsible.
Postmarket activities are equally important. Your obligations do not end at clearance. They include:
“Security maturity is not a destination. It is a practice. The companies that win long-term are the ones that treat each vulnerability, each incident, and each regulatory interaction as a learning opportunity rather than a threat to be managed.”
Reviewing the FDA cybersecurity requirements for startups gives you a clear picture of what the agency expects as your program matures.
Here is the uncomfortable truth: most health tech companies treat security risk assessment as a documentation exercise. They hire a consultant, generate a risk file, submit it to the FDA, and move on. The document sits in a shared drive and collects dust until the next submission cycle.
This approach fails for one fundamental reason. Adversaries do not read your risk file. They probe your actual device. And your actual device changes constantly, through software updates, new integrations, infrastructure migrations, and shifts in how clinicians actually use it in the field.
Real security is context-driven and dynamic. A risk assessment that was accurate at submission may be dangerously incomplete six months later. We have seen this pattern repeatedly: a company passes premarket review with a solid security file, then ships a firmware update that introduces a new communication interface, and nobody revisits the threat model because the compliance box was already checked.
The institutional blockers are often more stubborn than the technical ones. Engineering teams resist revisiting completed work. Compliance teams are focused on the next submission, not the last one. Leadership sees security spending as a cost center rather than a patient safety investment. These cultural dynamics are what avoiding FDA mistakes really requires you to address.
The companies that build genuinely secure devices share a few traits. They reward engineers who surface security concerns early, even when it delays a release. They run red team exercises that challenge their own assumptions. They treat every postmarket vulnerability report as a gift rather than a crisis. And they go beyond minimum requirements not because a regulator told them to, but because they understand that one serious exploit can destroy years of trust with hospital systems and patients.
The differentiation is real. Health systems increasingly ask vendors for detailed security documentation before procurement. A mature, well-documented security program shortens sales cycles and reduces the friction of enterprise security reviews. Security is not just a compliance cost. It is a market advantage.
If this article has surfaced gaps in your current security risk assessment program, the next step is validation by people who have done this before.
Testvox specializes in security testing for health tech companies navigating FDA readiness and EU MDR requirements. From threat modeling reviews to full penetration testing and fuzzing engagements, the team brings structured methodology and regulatory context to every assessment. Explore a detailed security testing guide that walks through how a patient monitoring device was prepared for FDA submission with end-to-end security validation. When you are ready to move from assessment to action, the security testing services page outlines how Testvox can tailor a program to your device type, deployment environment, and regulatory timeline. A focused consultation can turn your risk assessment from a compliance document into a genuine security asset.
Medical device risk assessments must tie every security finding directly to patient safety outcomes and satisfy regulatory requirements from the FDA and EU MDR, with the FDA’s SPDF guidance emphasizing exploitability over probability as the core risk measure. Standard software assessments rarely carry the same patient harm traceability requirement.
Deployment context significantly changes your CVSS scores because hospital environments include compensating controls that home environments lack. Research shows home environment scores can be up to 2.3 points higher than hospital scores for the same vulnerability, which directly affects your remediation priorities.
SPDF provides lifecycle governance, STRIDE structures your threat identification, and CVSS v4.0 BTE delivers context-driven scoring. The STRIDE and CVSS combination with an exploitability matrix gives you a complete, auditable foundation that regulators recognize.
Adopt a formal maturity framework, appoint a Chief Product Security Officer, and benchmark against industry peers using MDIC TPLC data. Organizations with dedicated security leadership consistently show higher maturity scores across all cybersecurity domains.
Probability models assume random failure, but attackers are intelligent and adaptive. CVSS BTE contextual scoring replaces probability with exploitability and severity of harm, which accurately reflects how adversarial threats actually behave in real deployment environments.
Let us know what you’re looking for, and we’ll connect you with a Testvox expert who can offer more information about our solutions and answer any questions you might have?