UAE
Testvox FZCO
Fifth Floor 9WC Dubai Airport Freezone

 22 April 2026
22 April 2026
 7:44 MIN Read time
7:44 MIN Read time
Nearly 25.1% of AI-generated code ships with confirmed vulnerabilities, and most development teams have no idea until something breaks in production. If you’re building software in India or the UAE, the threat landscape in 2026 is sharper and faster than anything we’ve seen before. Indian organizations face over 2,000 cyberattacks per week, which is 96% above the global average. The rules are changing: new data protection laws, AI-assisted development, and cloud-native architectures are forcing every CTO and founder to rethink how security testing actually fits into their build cycle.
| Point | Details |
|---|---|
| Adopt shift-left security | Catch vulnerabilities early in the development process for better outcomes. |
| Leverage new test methodologies | AI testing, CNAST, and API/MAST are critical for modern apps. |
| Prioritize by exploitability | Not all vulnerabilities matter equally—focus on what attackers can reach. |
| Stay compliant | Frequent, continuous testing helps meet India’s DPDPA and UAE regulations. |
The numbers make the case clearly. Security spending in India is projected to reach $3.4 billion in 2026, growing at 11.7%, and the average breach now costs Indian firms roughly ₹22 crore. That is not just a large enterprise problem. Startups and SMEs are frequently targeted because attackers know smaller teams tend to cut corners on security.
Regulation is adding another layer of pressure. India’s Digital Personal Data Protection Act (DPDPA) and the UAE’s equivalent frameworks now require organizations to demonstrate ongoing data protection compliance rather than relying on a one-time audit. Non-compliance carries serious financial and reputational penalties that no early-stage company can afford.
The costs of neglecting security testing go well beyond a single breach. They include customer churn, regulatory fines, remediation expenses, and delayed product launches. Traditional penetration testing performed once or twice a year simply cannot keep pace with monthly or biweekly release cycles.
Here is why the old approach falls short:
“Organizations that treat security as a continuous discipline rather than an annual event reduce breach impact by a measurable margin. Frequency and coverage together define modern security maturity.”
Looking at the security testing companies in India that are gaining traction, the consistent thread is continuous testing, automated coverage, and compliance alignment. These are not optional extras anymore. They are competitive requirements.
Understanding the alphabet soup of testing methods is the first step toward building a strategy that actually works. The core AST methodologies in 2026 include SAST, DAST, IAST, SCA, RASP, CNAST, and API/MAST testing. Each serves a distinct purpose.

| Method | What it tests | Best for | Key limitation |
|---|---|---|---|
| SAST | Source code (static) | Early dev stages | High false-positive rate |
| DAST | Running application | Pre-release validation | Misses source-level flaws |
| IAST | Code behavior at runtime | Agile and DevOps teams | Requires agent instrumentation |
| SCA | Open-source dependencies | Any team using OSS | Does not test custom code |
| RASP | Runtime self-protection | Production environments | Performance overhead |
| CNAST | Cloud-native infrastructure | Cloud-first startups | Specialized tool required |
| API/MAST | APIs and mobile surfaces | Fintech and e-commerce | Scope complexity |
For most startups and SMEs, trying to adopt all seven at once is impractical. Prioritize based on your stack and threat profile. Here is a practical sequence:
CNAST and API security are the fastest-rising priorities in 2026, especially for teams building on AWS, Azure, or GCP. API attacks now account for a significant share of all web breaches, and mobile-first markets like India demand that MAST is not an afterthought. Explore the full range of security testing methods to find the right starting point for your stack.
Pro Tip: Integrate SCA during the code review phase and pair it with RASP in production. SCA catches bad dependencies before they ship; RASP contains exploits if something slips through. Together, they cover both the entry and the exit point of most attack paths.
Shift-left is not a buzzword. It is the structural change that separates teams who find vulnerabilities in sprint reviews from teams who find them in breach reports. The core idea is simple: move security testing earlier in the development lifecycle, where fixing issues costs a fraction of what post-release patches do.
AI-generated code adds a wrinkle that many teams are not prepared for. Based on confirmed vulnerability rates across AI models, the risk picture looks like this:
| AI model / metric | Vulnerability rate |
|---|---|
| Average across models | 25.1% |
| GPT-5.2 (lowest observed) | 19.1% |
| Injection flaw rate | 33.1% |
| Most common flaw type | SSRF (Server-Side Request Forgery) |
This means that if your developers are using AI coding assistants without review controls, roughly one in four code blocks may carry a real vulnerability. SSRF alone can allow attackers to pivot from a public endpoint to internal services. The modern testing methods that catch these flaws must be embedded directly into the pipeline, not bolted on at the end.
Key advantages of adopting shift-left and continuous testing:
The AI testing tools gaining adoption in 2026 are specifically designed to flag AI-assisted code risks, not just traditional patterns. The impact of neglected testing compounds quickly in AI-heavy teams.
Pro Tip: Stop ranking vulnerabilities by CVSS (Common Vulnerability Scoring System) score alone. A critical CVSS rating on an unreachable code path is less urgent than a medium-rated flaw in a public payment API. Prioritize by exploitability and actual reachability in your specific environment.
Strategy without execution is just theory. Here is a practical rollout sequence built for teams with limited security headcount and tight release timelines.
For compliance alignment, keep these points in focus:
Two underestimated risks deserve direct attention in 2026. Business logic flaws, where an attacker exploits the intended behavior of your application rather than a technical bug, are harder to catch with automated tools and increasingly common. IaC misconfigurations, such as open S3 buckets or over-permissioned IAM roles baked into deployment templates, can scale a single mistake across your entire cloud infrastructure.
“Prioritize vulnerabilities based on exploitability and reachability in your specific context. A CVSS 9.8 in an internal-only library matters far less than a CVSS 6.5 in your public payment flow.”
Building a shared security culture matters just as much as tooling. Managing distributed security testing teams across dev, QA, and leadership requires clear ownership, not just good intentions.
Here is the uncomfortable truth: the teams that struggle most with application security are not the ones with too few tools. They are the ones with too many, configured poorly, generating noise that nobody has time to act on.
We have seen founders treat security testing as a procurement exercise. Buy the right platform, and the problem goes away. It does not. The real gains come from context and judgment, not coverage metrics. A tabletop exercise, where your team talks through what would actually happen if your payment API got compromised, will surface more actionable insight than a 200-page automated scan report that no one reads fully.
Shiny tech bias is real. Teams chase the newest AI-powered scanner while ignoring the business logic flaws that an attacker would exploit in twenty minutes of manual testing. Post-incident reviews, when done honestly, consistently reveal that the vulnerability was known or detectable. The gap is prioritization and accountability, not tooling. Browse in-depth security testing case studies to see where this plays out in practice.
For leaders ready to move from insight to action, Testvox brings a focused, hands-on approach to everything discussed here. Whether you are building a shift-left pipeline or need a full VAPT before your next funding round, we work with your team as a direct extension of your engineering org.
Our security testing services cover SAST, DAST, API security, and compliance alignment for both DPDPA and UAE standards. Our VAPT solutions go beyond checkbox audits to identify real exploitable weaknesses in your application and infrastructure. For teams building with AI, our AI testing case studies show how we validate AI-generated code risks before they reach production. Reach out to Testvox to build a security testing strategy that fits your release cadence and your risk profile.
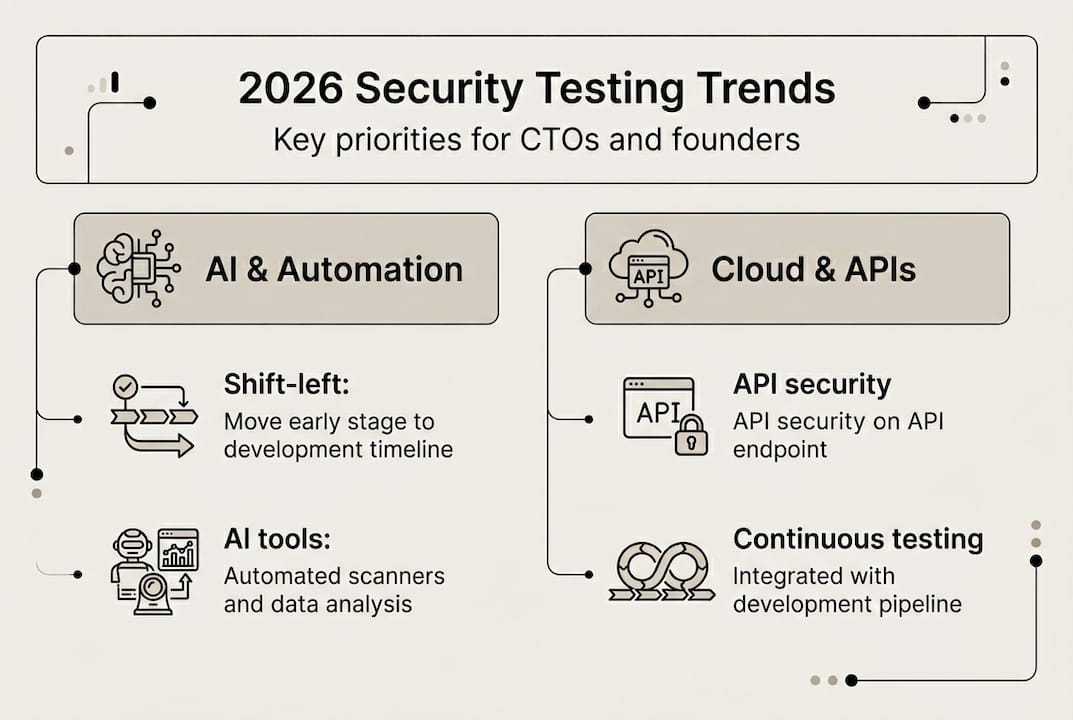
Leading trends include AI-based testing, shift-left security, continuous pen testing, cloud-native and API security, and compliance-driven frameworks aligned with SAST, DAST, IAST, SCA, RASP, CNAST, API/MAST testing methodologies.
Shift-left catches vulnerabilities during development rather than after release, which dramatically reduces fix costs and keeps pace with AI testing and continuous pen testing demands that fast-growing organizations face.
SSRF and injection flaws are especially prevalent, with over 25% of AI-generated code containing confirmed vulnerabilities across major models, making automated code review non-negotiable.
Startups should embed compliance checks directly into their CI/CD pipelines and commit to regular, continuous testing cycles that generate audit evidence aligned with DPDPA compliance and UAE data protection requirements.
Let us know what you’re looking for, and we’ll connect you with a Testvox expert who can offer more information about our solutions and answer any questions you might have?