UAE
Testvox FZCO
Fifth Floor 9WC Dubai Airport Freezone

 28 April 2026
28 April 2026
 10:55 MIN Read time
10:55 MIN Read time
Many founders building fintech platforms or e-commerce apps assume FDA cybersecurity rules are somewhere on their compliance checklist. They aren’t, at least not for most of you. FDA cybersecurity requirements apply exclusively to medical devices, including those with software (cyber devices), as defined under Section 524B of the FD&C Act. If you’re processing payments, running a lending platform, or managing an online marketplace, the FDA isn’t your regulator. But the line between fintech and health technology is blurring fast, and understanding where FDA authority starts could save your next product from a regulatory crisis.
| Point | Details |
|---|---|
| Not all startups are covered | FDA cybersecurity rules apply mainly to medical devices, not standard fintech or e-commerce platforms. |
| Understand eligibility | If your software diagnoses, monitors, or treats disease, you may qualify as SaMD and trigger FDA rules. |
| Follow core compliance steps | Integrate risk-based design, perform regular testing, and maintain full cybersecurity documentation to meet FDA demands. |
| Edge cases matter | Even legacy or non-networked software devices may be subject to some FDA cybersecurity actions. |
| Preparation enables growth | Early adoption of FDA-aligned practices helps startups pivot into digital health and stay ahead on security. |
Having established the scope at the outset, let’s zoom in on exactly who needs to worry about FDA cyber rules.
The FDA’s jurisdiction here is precise. Under Section 524B of the Federal Food, Drug, and Cosmetic (FD&C) Act, a “cyber device” is any medical device that includes software validated, installed, or authorized by the manufacturer; has the ability to connect to the internet; and contains technological characteristics that could be vulnerable to cybersecurity threats. All three conditions must apply. The definition is deliberately narrow because it focuses on patient safety, not data privacy in a general business sense.
Most fintech and e-commerce startups from India or the UAE are not subject to FDA rules unless their software qualifies as a medical device, such as Software as a Medical Device (SaMD) used for diagnosis, monitoring, or treatment of disease. Standard payments, lending products, and shopping platforms simply don’t meet that bar.
Where it gets tricky is at the edges of your product roadmap. Consider these scenarios:
The last one surprises most founders. If your analytics software influences clinical decisions, the FDA may classify it as SaMD regardless of whether you think of yourself as a “tech company.” Check the FDA’s common FDA cybersecurity mistakes guide to understand where startups misread their exposure.
Comparison: Standard product vs. SaMD eligibility
| Product type | FDA cyber device? | Key reason |
|---|---|---|
| Payment gateway app | No | No medical purpose or patient data |
| E-commerce marketplace | No | Commercial transactions only |
| Lending/credit scoring app | No | Financial data, not health |
| Wearable glucose monitor app | Yes | Diagnosis and monitoring of disease |
| AI diagnostic software | Yes | Clinical decision support with diagnosis intent |
| HSA + glucose tracker (integrated) | Possibly | Depends on intended use |
| Hospital inventory SaaS | Possibly | May influence clinical outcomes |
“If your software isn’t intended to diagnose, monitor, treat, cure, or prevent a disease or condition, the FDA has no cybersecurity authority over it. The moment you introduce that intent, even in marketing language, the regulatory picture changes entirely.”
The “intended use” principle is critical here. Founders sometimes inadvertently cross the line by making health-related claims in their pitch decks, app store descriptions, or marketing emails. The FDA evaluates the totality of your product’s presentation, not just its technical function. A fintech app that says “helps manage your diabetes costs” in its marketing copy is in a very different regulatory position than one that simply says “tracks medical expenses.”
Once you know if your startup is in scope, the next step is understanding what compliance involves.
The FDA’s framework is built around the idea that security must be baked into the product lifecycle, not patched on before submission. For startups that do fall within the cyber device definition, here are the core obligations structured around what you need to build, document, and submit.
1. Implement a Secure Product Development Framework (SPDF)
The FDA requires you to integrate a Secure Product Development Framework into your Quality Management System (QMS), specifically your QMSR under 21 CFR Part 820 or ISO 13485:2016. This means your entire build process, from design specs to release, must include security checkpoints. For a small team, this translates to documented threat modeling sessions, design reviews, and secure coding standards.
2. Conduct threat modeling and risk assessments
Before you write a single line of production code, map out your attack surface. Who could exploit your device? Through what vectors? With what consequences to a patient? This isn’t theoretical; regulators want documented evidence that you asked these questions and built mitigations.
3. Perform vulnerability assessment and penetration testing (VAPT)
VAPT is not optional for cyber devices. You need a structured vulnerability assessment identifying known weaknesses, followed by active penetration testing to validate those findings. Fixing device cybersecurity gaps before premarket submission is far less expensive than responding to a post-market recall. See also how security testing for FDA-ready patient devices works in practice.
4. Maintain a Software Bill of Materials (SBOM)
An SBOM is a full inventory of every software component in your product, including open-source libraries, third-party SDKs, and dependencies. SBOM maintenance is mandated under Section 524B(b)(3) for cyber devices. Think of it as a nutritional label for your software. When a new vulnerability is discovered in a library you use, you need to know immediately.
5. Premarket submission bundle
For 510(k), PMA, De Novo, or HDE submissions, cyber devices must include a defined set of documentation: plans and procedures for postmarket vulnerability monitoring and coordinated disclosure (524B(b)(1)); processes for providing reasonable assurance of cybersecurity throughout the product lifecycle, including updates and patches (524B(b)(2)); and the full SBOM (524B(b)(3)).
Key compliance milestones
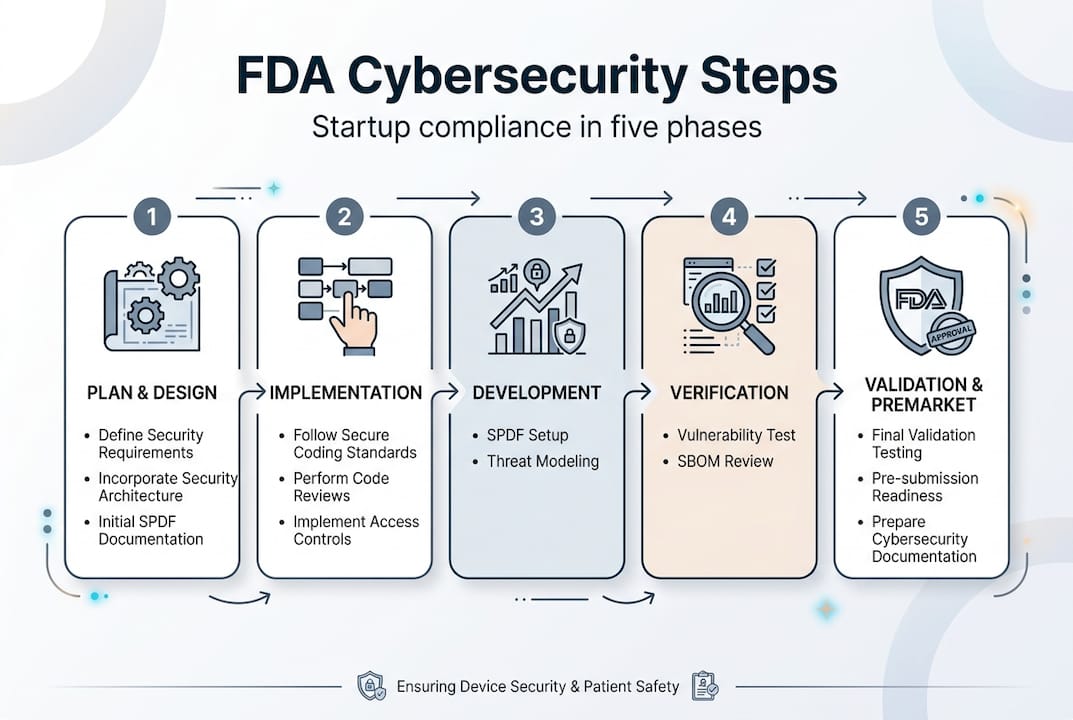
| Phase | Required action |
|---|---|
| Design | Threat modeling, architecture review |
| Development | Secure coding, SBOM tracking |
| Pre-release | VAPT, risk assessment documentation |
| Submission | Full cybersecurity bundle per 524B |
| Post-market | Ongoing monitoring, patching, disclosure |
Pro Tip: Start your SBOM on day one of development, not the week before submission. Retroactively cataloging dependencies in a complex codebase is one of the most expensive and error-prone compliance tasks a startup team faces.
With compliance requirements covered, what actions do startups need to take within their software and organization?
The FDA groups expected security controls into several broad categories. Understanding these categories helps small teams prioritize where to invest engineering time rather than trying to achieve perfect security across everything simultaneously.
Security control categories FDA expects in cyber devices:
These security control categories are the FDA’s way of saying security needs to be systemic, not a checklist of individual fixes.
For a startup with a lean engineering team, implementation doesn’t mean building all of this from scratch. Here’s how practical teams approach it:
Secure design: Use established frameworks like OWASP’s Secure Development Lifecycle. Even a two-engineer team can run a 90-minute threat modeling session using STRIDE methodology before each major feature sprint.
Cryptography: Don’t roll your own. Use industry-standard libraries (OpenSSL, libsodium) and default to TLS 1.3 for all communications. If your device uses Bluetooth, enforce Bluetooth LE Secure Connections.
Event logging: Cloud-native teams can use existing SIEM (Security Information and Event Management) tools such as AWS Security Hub or Azure Sentinel at startup-friendly pricing tiers. The key is logging the right events, not logging everything.

Patch management: Establish a vulnerability disclosure policy and a response SLA (service level agreement) before launch. When a CVE (Common Vulnerabilities and Exposures) entry hits a library you use, you should have a defined process to assess impact, test a patch, and push an update.
For a broader view of where the security landscape is heading in 2026, review the emerging cybersecurity trends shaping how regulated and non-regulated tech teams are building defenses. A practical step-by-step cybersecurity guide for smaller organizations is also useful for teams building out their first security program.
Pro Tip: The single most common oversight for startup teams is skipping logging and monitoring until scaling pressure forces them to act. For regulated devices, inadequate audit trails at premarket review can delay your 510(k) submission by months. Build logging infrastructure before your beta.
Real-world innovation is rarely simple; let’s dive into special cases and how FDA guidance adapts to startup realities.
Some of the most difficult compliance questions come from founders who are building genuinely novel products. Here are four situations where FDA cybersecurity requirements surface unexpectedly.
1. Non-networked legacy devices with software
Founders who acquire or modify existing medical devices sometimes assume that a device without active internet connectivity is outside FDA cyber scope. This is wrong. Non-networked devices with software still require cybersecurity assessment if they contain software and could be connected via physical media or indirect means. If you’re building an app that interfaces with an older medical monitor via USB, you may inherit compliance obligations.
2. Legacy device modifications
Modifying a predicate device in a 510(k) submission triggers new cybersecurity documentation requirements. Even a minor software update to an existing cleared device must be assessed for cybersecurity impact. Changes that seem unlikely to affect security still require a documented assessment to confirm that conclusion.
3. AI and ML-enabled devices
AI/ML software used for diagnostic or treatment purposes is one of the fastest-growing SaMD categories. The FDA has issued guidance on Predetermined Change Control Plans (PCCPs), which let manufacturers pre-specify how their AI model will change over time without requiring a new submission for each update. This is critical for startups building adaptive diagnostic algorithms.
4. Scaling documentation with risk
One of the most common misconceptions is that FDA compliance is a fixed, monolithic burden that small companies can’t sustain. Guidance actually emphasizes risk-based documentation that scales with cybersecurity risk, not device class or company size. A low-risk, limited-function SaMD requires proportionally less documentation than a networked ICU monitor. For our VAPT case studies, you can see how documentation scope is calibrated to actual risk profiles.
“The FDA’s risk-based approach means a startup isn’t competing with a multinational’s compliance budget. You’re competing with the depth of your own threat analysis. A thoughtful small team can meet premarket requirements that a poorly organized large team would fail.”
The real tension for founders is not compliance cost. It’s the cognitive overhead of building a regulated product in a startup environment where priorities shift weekly. Founders who treat cybersecurity documentation as a parallel workstream, updated alongside each sprint, consistently report lower compliance stress than those who batch it all at the end. For more on how security controls fit modern innovation cycles, check out top IT security essentials that apply regardless of your regulatory environment.
Having unpacked the operational details, here’s why FDA-ready thinking matters even if your startup isn’t regulated yet.
Regulatory boundaries shift. The fintech startup processing wellness app payments today could be the digital therapeutics platform seeking FDA clearance in three years. Founders in India and the UAE building at the intersection of financial services and health data are particularly exposed to this trajectory, because both markets are seeing rapid convergence between health insurance technology, patient financing, and connected monitoring.
The FDA’s security framework, including threat modeling, SBOM management, VAPT, and lifecycle monitoring, isn’t just a regulatory checklist. It’s a genuinely superior way to build secure software. Startups that adopt this discipline early protect their customers, reduce breach liability, and build institutional knowledge that becomes a competitive moat when regulation eventually arrives at their door.
We’ve seen this pattern with our fintech testing insights: teams that build with FDA-grade rigor even when not required consistently ship fewer critical vulnerabilities, pass enterprise security audits faster, and close B2B deals with regulated counterparties more easily. The cost of adoption early is low. The cost of retrofitting compliance onto a product already in production is very, very high.
Don’t wait for a regulatory notice to build like it matters.
For hands-on help, here’s how our solutions accelerate readiness for audits and peace of mind.
Whether your startup is today’s payment platform or tomorrow’s digital health product, security testing gaps are expensive to ignore. Testvox brings specialized security testing services including VAPT, threat modeling support, and OWASP-aligned assessments to fintech and e-commerce teams across India and the UAE.
If you’re building or scaling an e-commerce platform, our comprehensive e-commerce tests checklist covers the security and functional gaps most teams miss before launch. For payment-heavy fintech products, our fintech app testing best practices resource maps real-world risks to testable controls. When compliance confidence is on the line, our “One-Round Complete Testing” approach gives you a single deep-dive audit that covers everything before your beta goes live.
No, unless your software is classified as a medical device for diagnosis or treatment, FDA cybersecurity rules do not apply to standard fintech or e-commerce products.
A cyber device is a medical device that includes software, connects to the internet, and contains technology that may be vulnerable to cybersecurity threats, all three conditions must be present.
No formal exemptions exist, but required documentation scales with the level of cybersecurity risk your device presents, not your company size or device classification tier.
Integrate FDA-aligned security frameworks such as SPDF and SBOM tracking into your current development process so the documentation and architecture are already in place when a pivot happens.
Yes, software-enabled devices and some non-networked products still require a cybersecurity impact assessment and relevant documentation even if they lack direct internet connectivity.
Let us know what you’re looking for, and we’ll connect you with a Testvox expert who can offer more information about our solutions and answer any questions you might have?